Author: Karlo Smid
Reading Club, Practical Guide For macOS Privacy And Security
reading club, security testing
TL;DR A practical step by step security and privacy guide for macOS. Who Several contributors. Why You will learn about security testing for the operating system and how to do…
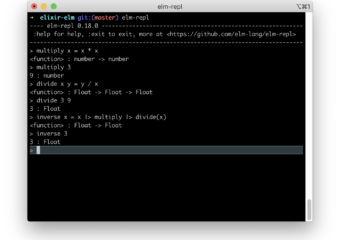
How To Use Elm Pipe Operator
TL;DR In the previous post, we learned how to use the JSON decoder in Elm REPL. Today we move on to practical usage of Elm pipe operator. This post is…
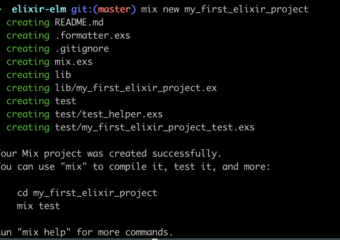
Three Ways How To Run Elixir Script
elixir, functional programming
TL;DR In the previous post, we presented how to run pure Erlang functions from Elixir. Today we explain three ways how to run Elixir script. This post is part of…
What Is Coverage Criterion In Software Testing
BBST Foundations, introduction
TL;DR In the previous post, we explained what the test requirement is? Today we discuss the coverage criterion. We will introduce you to software testing based on the remarkable book, …
Properties Of A Good Testing Taxonomy
BBST Foundations, introduction
TL;DR Now that we know who uses Taxonomies using this excellent paper: Bug Taxonomies: Use Them to Generate Better Tests [Vijayaraghavan, Kaner]. Let’s explore the properties of a good testing…
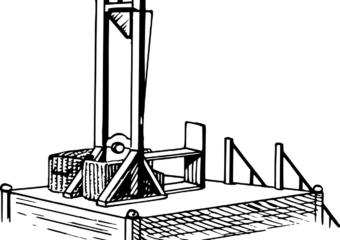
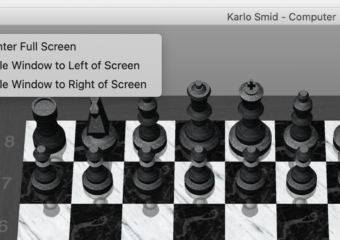
Apple UX Inconsistency
TL;DR We continue our testing from the trenches series by finding random issues. This time, we present you with a macOS UX inconsistency. The Problem The problem is clearly depicted…
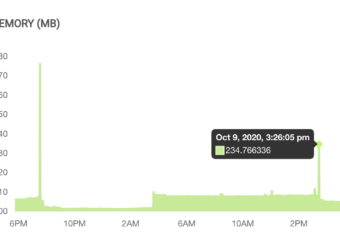
Reading Club, Practical Web Cache Poisoning
TL;DR In this reading club, we gave you an extensive example of a web cache poisoning attack. You will also learn how Web Cache works. And one extra feature for…