Testing From Trenches, When Output Is List Of Commands
test strategy, testing from tranches, Uncategorized
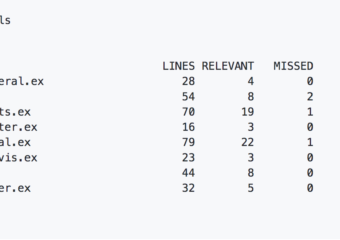
TL;DR This week’s testing from the trenches story explains our test strategy for software that generates other software commands. Test Strategy For Generated Commands Imagine a complicated system that creates…